We are thrilled to announce that our workshop paper entitled “Large-Scale Analysis of Malware Distribution via Fake Game Cheats and Cracked Software on YouTube” has been accepted for publication in the 5th Workshop on Attackers and Cyber-Crime Operations (WACCO 2026), co-located with IEEE EuroS&P 2026. Congratulations Yamagishi-kun!
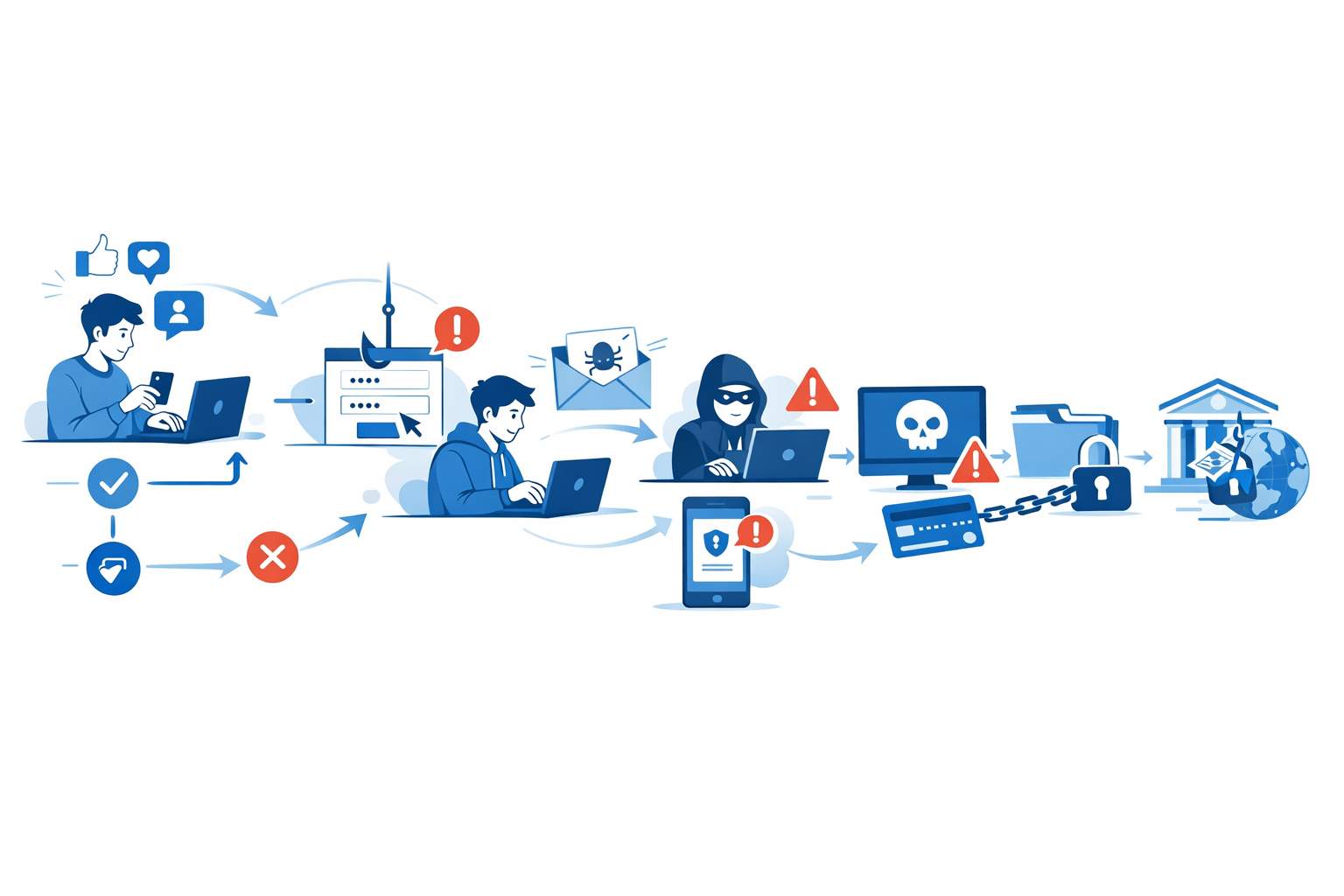
In this work, we present VIPER (VIdeo Platform Exploitation Reconnaissance), an automated system that continuously monitors YouTube for malware distribution campaigns masquerading as game cheats or cracked software—a class of threat we term VidCrackBait. VIPER iteratively updates its search queries to track evolving attack patterns and harvests video metadata via the YouTube Data API v3. Over five months, VIPER collected 104,974 videos from 38,855 unique channels, identifying 6,976 distinct fully qualified domain names embedded in descriptions and comments. Our analysis reveals that attackers target popular competitive games with recurring title/description/thumbnail patterns, and we identify 396 intermediate YouTube channels that post no content but serve as persistent relay nodes—forming multi-stage redirection chains that link YouTube to messaging platforms, file-hosting services, and social media.
Rei Yamagishi, Shota Fujii, and Tatsuya Mori, "Large-Scale Analysis of Malware Distribution via Fake Game Cheats and Cracked Software on YouTube." In Proc. of the 5th Workshop on Attackers and Cyber-Crime Operations (WACCO 2026), co-located with IEEE EuroS&P 2026, Venice, Italy, Jun 2026.